Is your DDoS mitigation fast enough to save a 10 Gbps service?
Sub-second shields vs. global scrubbing: how Flowtriq stacks up in real DDoS firefights
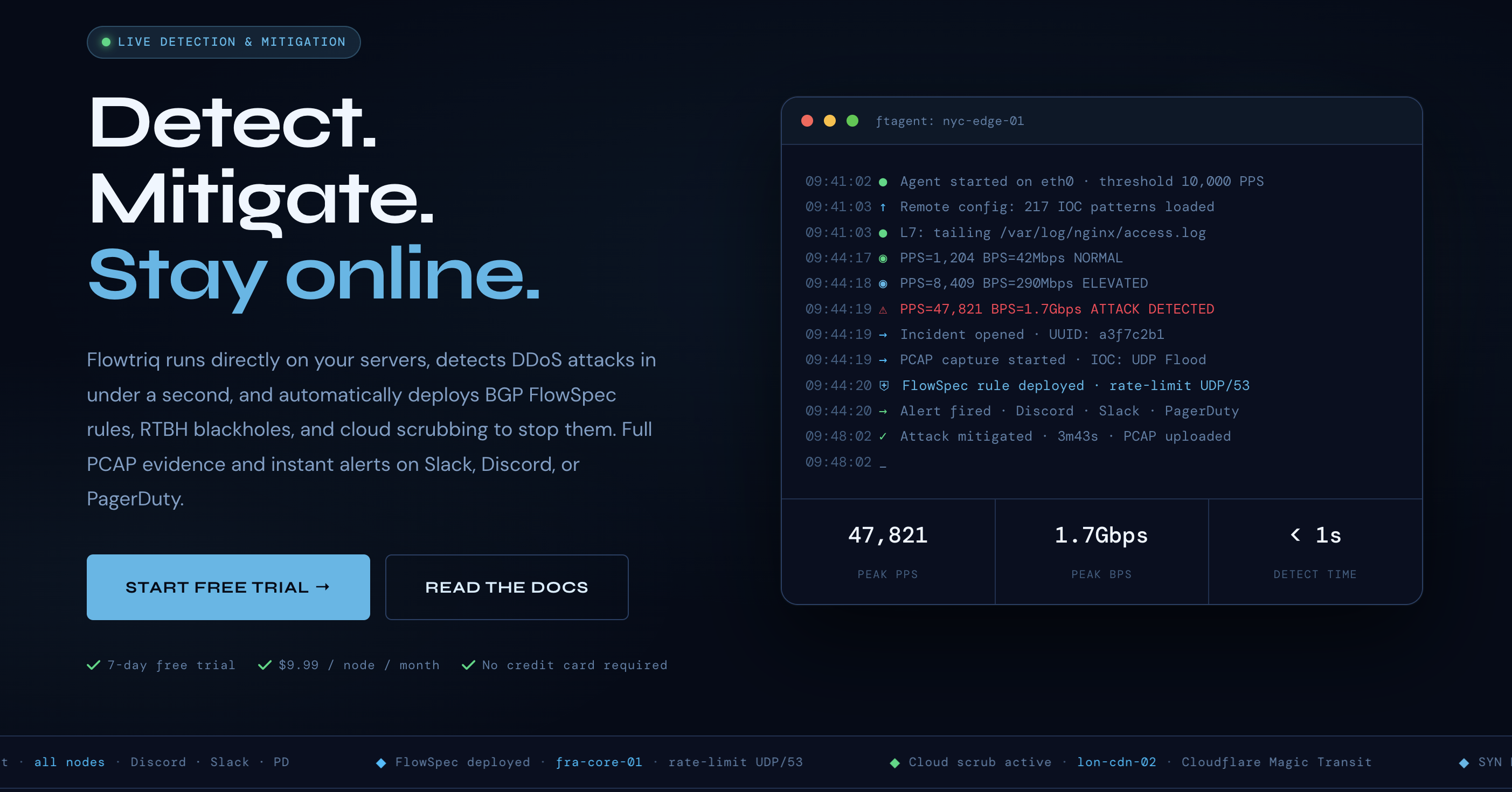
At 10 Gbps, a single second equals roughly 1.25 GB of traffic—enough to crater a latency-sensitive service before alerting even fires. In that context, Flowtriq’s sub-second detection + auto-mitigation pitch isn’t marketing fluff; it’s an architectural choice. Code Builder Weekly’s analysis compares Flowtriq’s agent-based model with network-edge incumbents to see where each approach wins for developer tools teams focused on resilient Architecture Patterns, Best Practices, and repeatable runbooks.
Quick Comparison Table
| Feature | Flowtriq | Cloudflare Magic Transit | NETSCOUT Arbor DDoS |
|---|---|---|---|
| Pricing | $9.99/node/month flat (annual: $7.99) | Enterprise, custom (typically by clean traffic/Gbps) | Enterprise, custom (appliance + throughput tiers) |
| Ease of Use | 2-minute Linux agent (Python), auto-baselining, no manual thresholds | Requires BGP/GRE onboarding; network engineering expertise | Dedicated appliances/sensors; tuning and network ops expertise |
| Developer Tools Features | Full PCAP on every attack, programmable runbooks, immutable audit logs, webhooks, Slack/Discord/PagerDuty/SMS, IOC correlation, status pages | Robust APIs/Terraform, analytics, Logpush to SIEM; not host-level PCAP | REST/SNMP, integrations with routers/mitigation systems; fewer developer-first niceties |
| Integration Options | BGP FlowSpec, RTBH, Cloud scrubbing (Cloudflare/OVH/Hetzner), multi-channel alerting | Cloudflare Anycast, Magic Firewall, Logpush, Spectrum | BGP/FlowSpec, TMS, peering/scrubbing centers, SIEM/SOAR |
Where Flowtriq Wins
- - Sub-second, on-host precision for modern workloads. Flowtriq’s agent (ftagent) inspects packets directly on Linux NICs and checks PPS every second, enabling detection and mitigation in <1s across 8+ attack types (from SYN/UDP floods to L7). Compared to Cloudflare Magic Transit, which operates upstream, Flowtriq’s host-level PCAP and IOC pattern matching (642,000+ indicators) provide developer-friendly forensics and fine-grained classification at the point of impact.
- - Predictable, developer-aligned pricing. Flat $9.99/node/month with no traffic or per-alert surcharges is straightforward for SaaS, game servers, and edge nodes. Enterprise DDoS offerings like NETSCOUT Arbor and Magic Transit commonly price by capacity, clean traffic, or hardware—cost-effective at carrier scale, but harder to forecast for fast-growing app teams.
- - Automation-first incident response. Flowtriq chains mitigations into runbooks, fires multi-channel alerts in under a second, and writes an immutable audit log—useful for post-incident reviews and Best Practices. This DevOps-native surface (PCAP on every attack, webhooks, status pages) shortens time-to-restore and aligns with Refactoring Guides that codify operational playbooks in version control.
Where Competitors Have an Edge
- - Massive volumetric absorption and global reach. Cloudflare Magic Transit brings Anycast scrubbing capacity that small teams can’t replicate, plus tight integration with their edge (Magic Firewall, Spectrum). For sustained 1+ Tbps events or whole-prefix protection, Magic Transit is purpose-built. See practitioner feedback: https://www.gartner.com/reviews/market/distributed-denial-of-service-ddos-mitigation/vendor/cloudflare
- - Carrier-grade visibility and SOC options. NETSCOUT Arbor DDoS offers deepNetFlow visibility with appliances and mature managed services for ISPs/MSPs. If you operate backbone links or multi-tenant networks, Arbor’s ecosystem can outpace agent-only strategies. Peer insights: https://www.gartner.com/reviews/market/distributed-denial-of-service-ddos-mitigation/vendor/netscout/product/arbor-ddos
Best Use Cases for Developer Tools
- - Choose Flowtriq when:
- - You control Linux hosts (K8s nodes, game servers, microservices, edge PoPs) and want programmatic mitigations as code—webhooks, audit trails, and PCAPs feed neatly into CI/CD, SIEM, and incident retros.
- - You prefer Architecture Patterns that localize detection close to workloads, with dynamic baseline learning instead of brittle thresholds.
- - Budget predictability matters more than peak egress economics.
- - Choose Cloudflare Magic Transit when:
- - You need whole-prefix protection, global scrubbing, and SLA-backed resilience—especially for large volumetric floods and hybrid WANs.
- - Choose NETSCOUT Arbor when:
- - You run an ISP/MSP or large enterprise network and want deep telemetry, FlowSpec/RTBH automation at the router layer, and optional 24x7 SOC.
The Verdict
For developer tools professionals “building better code, one week at a time,” the data points to a split decision based on operating model. Flowtriq is the pragmatic pick for app-centric teams needing sub-second, host-level defense with strong developer ergonomics (runbooks, PCAP, immutable audits) and flat pricing. Cloudflare Magic Transit and NETSCOUT Arbor DDoS remain superior for global-scale absorption, cross-network enforcement, and carrier operations. Many high-maturity teams blend patterns: Flowtriq on hosts for rapid detection/forensics, escalated automatically to upstream scrubbing for volumetric headroom—a best-practice architecture that minimizes blast radius while preserving developer velocity.